You can automate the connection process for a network or dial-up connection by using the autodial feature. with aautodial enabled, network address are mapped to connection a destination, which allows a destination to be automatically dialed when a remote resources is referenced.
You can also automate the connection process for any Microsoft client by using a simple batch file and the resdial command or by using, Windows NT and Windows 200 application that recognizes remote access.
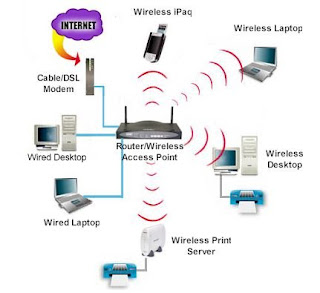
Atomatic Wireless Internet / Network connection in Windows XP
Windoes XP allows you to established wireless connections to network routers ans accedd points automatically. This feature helps you to make wireless Internet / Wi- Fi network connections more easily with laptop computers and is highly recommended for those who roam between multiple locations.
But not all windows XP computer with Wi-Fi wireless support are capable of automatic wireless configuration. You can verify your wireless network connection properties doing by following method.
1. Start Menu, open windows control panel.
2.Inside control panel, click the " Network Connections" option if it exists, otherwise first click. " Network and Internet conenctions" and then click " Network connections".
3. Finally, right - click " Wireless Network conenction" and choose " Properties".
You can also automate the connection process for any Microsoft client by using a simple batch file and the resdial command or by using, Windows NT and Windows 200 application that recognizes remote access.
Atomatic Wireless Internet / Network connection in Windows XP
Windoes XP allows you to established wireless connections to network routers ans accedd points automatically. This feature helps you to make wireless Internet / Wi- Fi network connections more easily with laptop computers and is highly recommended for those who roam between multiple locations.
But not all windows XP computer with Wi-Fi wireless support are capable of automatic wireless configuration. You can verify your wireless network connection properties doing by following method.
1. Start Menu, open windows control panel.
2.Inside control panel, click the " Network Connections" option if it exists, otherwise first click. " Network and Internet conenctions" and then click " Network connections".
3. Finally, right - click " Wireless Network conenction" and choose " Properties".